Installing DFIR-IRIS on FreeBSD using Jails
This is a live blogging of the installation process of DFIR-IRIS on FreeBSD 14.0-RELEASE using Jails and Jailer.
The main requirements are:
- Nginx
- PostgreSQL
- Python
- Some random dependencies we saw in the Dockerfile
I assume you already have nginx up and running, we will just be setting up a vhost under the domain name dfir.cert.am. Don’t worry, this is INSIDE our infrastructure, you will not be able to connect to it 🙂
First we create a jail named iris0, using Jailer:
jailer create iris0
Next we install the required software inside of the jail. Looks like everything is available in FreeBSD packages:
jailer console iris0<h2>Installing DFIR-IRIS</h2>
pkg install \ nginx \ python39 \ py39-pip \ gnupg \ 7-zip \ rsync \ postgresql12-client \ git-tiny \ libxslt \ rust \ acme.sh
Since we’re using FreeBSD, we’ll be doing things the right way instead of the Docker way, so we will be running IRIS as a user, not as root.
pw user add iris -m
Next we setup some directories and checkout the repo
root@iris0:~ # pw user add iris -m
root@iris0:~ # su - irisiris@iris0:~ $ git clone --branch v2.4.7 https://github.com/dfir-iris/iris-web.git iris-web
Finally, we install some python dependencies using pip.
iris@iris0:~ $ cd iris-web/source
iris@iris0:~/iris-web/source $ pip install -r requirements.txt
Now we have to configure the .env
# -- DATABASEexport POSTGRES_USER=postgresexport POSTGRES_PASSWORD=postgresexport POSTGRES_DB=iris_dbexport POSTGRES_ADMIN_USER=irisexport POSTGRES_ADMIN_PASSWORD=longpasswordexport POSTGRES_SERVER=localhostexport POSTGRES_PORT=5432# -- IRISexport DOCKERIZED=0export IRIS_SECRET_KEY=verylongsecretexport IRIS_SECURITY_PASSWORD_SALT=verylongsaltexport IRIS_UPSTREAM_SERVER=app # these are for docker, you can ignoreexport IRIS_UPSTREAM_PORT=8000# -- WORKERexport CELERY_BROKER=amqp://localhost# Set to your rabbitmq instance# Change these as you need them.# -- AUTH#IRIS_AUTHENTICATION_TYPE=local## optional#IRIS_ADM_PASSWORD=MySuperAdminPassword!#IRIS_ADM_API_KEY=B8BA5D730210B50F41C06941582D7965D57319D5685440587F98DFDC45A01594#IRIS_ADM_EMAIL=admin@localhost#IRIS_ADM_USERNAME=administrator# requests the just-in-time creation of users with ldap authentification (see https://github.com/dfir-iris/iris-web/issues/203)#IRIS_AUTHENTICATION_CREATE_USER_IF_NOT_EXIST=True# the group to which newly created users are initially added, default value is Analysts#IRIS_NEW_USERS_DEFAULT_GROUP=# -- LISTENING PORT#INTERFACE_HTTPS_PORT=443<h2>Configuring HTTPS</h2>
We can use acme.sh to issue a TLS certificate from Lets Encrypt.
root@iris0:~ # acme.sh --set-default-ca --server letsencryptroot@iris0:~ # acme.sh --issue -d dfir.cert.am --standaloneroot@iris0:~ # acme.sh -i -d dfir.cert.am --fullchain-file /usr/local/etc/ssl/dfir.cert.am/fullchain.pem --key-file /usr/local/etc/ssl/dfir.cert.am/key.pem --reloadcmd 'service nginx reload'<h2>Setup nginx</h2>
DFIR-IRIS provides a nginx configuration template at nginx.conf, we will be using that, with a little bit of modifications.
The final nginx.conf will look like this:
#user nobody;worker_processes 1;# This default error log path is compiled-in to make sure configuration parsing# errors are logged somewhere, especially during unattended boot when stderr# isn't normally logged anywhere. This path will be touched on every nginx# start regardless of error log location configured here. See# https://trac.nginx.org/nginx/ticket/147 for more info. ##error_log /var/log/nginx/error.log;##pid logs/nginx.pid;events { worker_connections 1024;}http { include mime.types; default_type application/octet-stream; # Things needed/recommended by DFIR-IRIS map $request_uri $csp_header { default "default-src 'self' https://analytics.dfir-iris.org; script-src 'self' 'unsafe-inline' https://analytics.dfir-iris.org; style-src 'self' 'unsafe-inline';"; } server_tokens off; sendfile on; tcp_nopush on; tcp_nodelay on; types_hash_max_size 2048; types_hash_bucket_size 128; proxy_headers_hash_max_size 2048; proxy_headers_hash_bucket_size 128; proxy_buffering on; proxy_buffers 8 16k; proxy_buffer_size 4k; client_header_buffer_size 2k; large_client_header_buffers 8 64k; client_body_buffer_size 64k; client_max_body_size 100M; reset_timedout_connection on; keepalive_timeout 90s; client_body_timeout 90s; send_timeout 90s; client_header_timeout 90s; fastcgi_read_timeout 90s; # WORKING TIMEOUT FOR PROXY CONF proxy_read_timeout 90s; uwsgi_read_timeout 90s; gzip off; gzip_disable "MSIE [1-6]\."; # FORWARD CLIENT IDENTITY TO SERVER proxy_set_header HOST $http_host; proxy_set_header X-Forwarded-Proto $scheme; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; # FULLY DISABLE SERVER CACHE add_header Last-Modified $date_gmt; add_header 'Cache-Control' 'no-store, no-cache, must-revalidate, proxy-revalidate, max-age=0'; if_modified_since off; expires off; etag off; proxy_no_cache 1; proxy_cache_bypass 1; # SSL CONF, STRONG CIPHERS ONLY ssl_protocols TLSv1.2 TLSv1.3; ssl_prefer_server_ciphers on; ssl_certificate /usr/local/etc/ssl/dfir.cert.am/fullchain.pem; ssl_certificate_key /usr/local/etc/ssl/dfir.cert.am/key.pem; ssl_ecdh_curve secp521r1:secp384r1:prime256v1; ssl_buffer_size 4k; # DISABLE SSL SESSION CACHE ssl_session_tickets off; ssl_session_cache none; server { listen 443 ssl server_name dfir.cert.am; root /www/data; index index.html; error_page 500 502 503 504 /50x.html; add_header Content-Security-Policy $csp_header; # SECURITY HEADERS add_header X-XSS-Protection "1; mode=block"; add_header X-Frame-Options DENY; add_header X-Content-Type-Options nosniff; # max-age = 31536000s = 1 year add_header Strict-Transport-Security "max-age=31536000: includeSubDomains" always; add_header Front-End-Https on; location / { proxy_pass http://localhost:8000; location ~ ^/(manage/templates/add|manage/cases/upload_files) { keepalive_timeout 10m; client_body_timeout 10m; send_timeout 10m; proxy_read_timeout 10m; client_max_body_size 0M; proxy_request_buffering off; proxy_pass http://localhost:8000; } location ~ ^/(datastore/file/add|datastore/file/add-interactive) { keepalive_timeout 10m; client_body_timeout 10m; send_timeout 10m; proxy_read_timeout 10m; client_max_body_size 0M; proxy_request_buffering off; proxy_pass http://localhost:8000; } } location /socket.io { proxy_set_header Host $http_host; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header X-Forwarded-Proto $scheme; proxy_http_version 1.1; proxy_buffering off; proxy_set_header Upgrade $http_upgrade; proxy_set_header Connection "Upgrade"; proxy_pass http://localhost:8000/socket.io; } }}<h2>Setup PostgreSQL</h2>I assume you know how to do this 🙂 You don’t need to configure a separate user, by the looks of it, IRIS likes to do that itself. Thanks to Jails I was able to run a separate PostgreSQL instance in the iris0 jail.
P.S. If you are running PostgreSQL inside a jail, make sure that the following variables are set in your jail configuration
sysvshm = new; sysvmsg = new;<h2>Running DFIR-IRIS</h2>
Now that everything is up and running, we just need to run DFIR-IRIS and it will create the database, needed users, an administration account, etc.
su - iriscd ~/iris-web/source. ../.env~/.local/bin/gunicorn app:app --worker-class eventlet --bind 0.0.0.0:8000 --timeout 180 --worker-connections 1000 --log-level=debug
Assuming everything is fine, now we can setup a rc.d service script to make sure it runs at boot.
For that I wrote two files, the service itself and a helper start.sh script
rc.d script at /usr/local/etc/rc.d/iris
#!/bin/sh# PROVIDE: iris# REQUIRE: NETWORKING# KEYWORD: . /etc/rc.subrname="iris"rcvar="iris_enable"load_rc_config ${name}: ${iris_enable:=no}: ${iris_path:="/usr/local/iris"}: ${iris_gunicorn:="/usr/local/bin/gunicorn"}: ${iris_env="iris_gunicorn=${iris_gunicorn}"}logfile="${iris_path}/iris.log"pidfile="/var/run/${name}/iris.pid"iris_user="iris"iris_chdir="${iris_path}/source"iris_command="${iris_path}/start.sh"command="/usr/sbin/daemon"command_args="-P ${pidfile} -T ${name} -o ${logfile} ${iris_command}"run_rc_command "$1"and the helper script at /home/iris/iris-web/start.sh
#!/bin/shexport HOME=$(getent passwd `whoami` | cut -d : -f 6). ../.env${iris_gunicorn} app:app --worker-class eventlet --bind 0.0.0.0:8000 --timeout 180 --worker-connections 128now we set some variables in rc.conf using sysrc and we can start the service.
sysrc iris_enable="YES"sysrc iris_path="/home/iris/iris-web"sysrc iris_gunicorn="/home/iris/.local/bin/gunicorn"
Finally, we can start DFIR-IRIS as a service.
service iris start
Aaaaand we’re done 🙂
Thank you for reading!
There are some issues that I’d like to tackle, for example, service iris stop doesn’t work, and it would be nice if we ported all of the dependencies into Ports, but for now, this seems to be working fine.
Special thanks to the DFIR-IRIS team for creating this cool platform!
That’s all folks…
https://antranigv.am/posts/2024/05/dfir-iris-freebsd-jail/
#DFIR #FreeBSD #HowTo #InfoSec #IRIS #Jailer #Jails #PostgreSQL #Python
@mms https://github.com/charliemaiors/freebsd-ansible -- there are a few plays with tasks related to automatically updating bare metal and #jails. Haven't tested these yet, but they look promising. This kind of infrastructure management is necessary for managing #FreeBSD at scale. #Puppet and salt stack might be good alternatives if you don't #Ansible. See also : https://docs.ansible.com/ansible/latest/os_guide/intro_bsd.html
@PurpleJillybeans
1. It works. At least for me.
2. It has #ZFS fully integrated. Boot environments work on top of that, they're very useful for a desktop as well. Similar for #jails, although admittedly a bit less relevant on desktops.
3. It's "designed". The whole base system is a well-integrated piece of software from a single source repository. You can easily understand how it works (at least from the user perspective). Changes are done in a thoughtful way, not "just because", and not in isolation with no "big picture" in mind like you often see in the GNU/Linux ecosystem.
4. When I use it on my server anyways, using something else for my desktop would just be unnecessary friction for me.
More of my reasons: https://sekrit.de/webdocs/freebsd/advocacy.html
Yes, I used some Linux system before. Getting increasingly frustrated with it around 10 years ago (yes, #systemd had its share, but wasn't the only thing), I looked for something better. I quickly became a #FreeBSD ports contributor and later commiter.
Hey #BSD Fans!
We all share the same interests - #BSD based systems like #FreeBSD, #OpenBSD and #NetBSD.
We chat all day, sharing thoughts, questions and help. We talk on Matrix across different channels, we share on the #Fediverse. We have @vermaden@bsd.cafe's newsletter, we have @dexter@bsd.network's #FreeBSD #Jails and #bhyve calls and many other ones I can't list here.
Wondering if there would be and interests in the #BSDNetwork, #BSDCafe, etc., for a weekly smalltalk session like in a pub. Just a Jitsi based video/audio call where we can meet, discuss things from newsletter, trending things from the #Fediverse or just have off-topic and openminded discussions. This could result into the #BSDPub meeting.
I know, some people are shy - keep your cam off until you feel comfortable and feel free to join the discussions. Even this meetings should make fun and no pressure - so if someone is not in the mood or can't make it - no worries. No one will judge.
Would you be interested?
#helloSystem #DragonFlyBSD #HardenedBSD #GhostBSD #pfSense #illumos #tribblix #solaris #opensolaris #zfs #community #social
| Yes: | 44 |
| No: | 4 |
Closed
A: Using my 4x #RV64 #VisionFive2 boards - each board has 8GB. This could lead into a temporary and time limited, dedicated usage of 7-30d.
B: It could be shared across with 7 users by #jails on #FreeBSD. Requires better support in FreeBSD.
C: QEMU emulated instances running on amd64
I’d really like to see rv64 being pushed and it was excactly the reason to get those boards to get more experience on that platform. However, just sharing some ideas - it does not mean that they will be available in the near future (but would be cool if so).
Now, I’m running a friendly beta test within the #BSD Community (primary #BSDCafe & BSD fans) for free small sized hosted #VMs / #Jails (IPv6 only).
The first system is already full. Let’s see how this will be (ab)used?! Maybe, the next stack will start after Easter.
#FreeBSD 13.3 deployed at home. 4 times "metal", one VM, 12 #VNET #jails.
First time ever not the vanilla version from the releng branch (with just one commit adding kernel configs on top), but pulling in extra patches from some repo on github. 🙄 Because it's unusable in my setup otherwise 😞.
I really really hope this will stay a rare exception for FreeBSD. And of course I hope for an EN including the functionality of all these patches I now pulled in myself ... would probably be a PITA having to maintain them locally.
It's Saturday!
Got a message from a colleague I haven't heard from in a while. They're asking for a quote for hosting an e-commerce site they've built with a friend, who by the way sells products I love.
Offered them hosting based on FreeBSD and jails, and they're eager to proceed, trusting the technical solution. Starting right away with enthusiasm, looking forward to heading downtown. It's cold outside but thankfully no rain. Another good day! 😊
#Hosting #Ecommerce #FreeBSD #Jails #TechSolution #WeekendVibes
New #BSD #homelab project on the horizon. 🙂
Using one of my #thinkcentre models as a #NAS to cut the costs of running a full bore i5 PC.
I currently have two #ssd disks in there - #ZFS mirror.
I do not need the mirror setup at home. I rather have backups than high avilability here.
So, the #thinkcentre will be a jack of all trades to some extent.
Serving #Jails and file sharing via #Samba and #NFS
I think I should dedicate a blog post to the setup after finishing it 😎
#FreeBSD truly is the power to serve! 
@marquito Pors sind (über lange Zeit) von DEM Weg, 3rd-party Software auf einem BSD-System zu installieren (weil's gar nicht anders ging), zum flexiblen Paketbausystem geworden. Das muss natürlich aus dem Source bauen, wie bei jeder anderen Softwaredistribution. Der "Ansatz" ist jedenfalls schon lange nicht mehr, alles "frisch" zu kompilieren ... zumindest für Tier-1 Architekturen ist der bevorzugte Weg für User pkg, also Binary-Pakete.
Für User, die trotzdem selbst bauen wollen (weil sie andere Build-Konfigurationen wollen) gibt's mit poudriere ein mächtiges und flexibles Tool, das das eigene Repository für pkg baut, aus dem dann installiert werden kann. Dabei sorgen isolierte builds (ein jail pro build) für zuverlässig reproduzierbare Ergebnisse und für Pakete die von den angepassten Konfigurationen nicht betroffen sind kann direkt ein offizielles Paket runtergeladen und ins eigene Repository gelegt werden statt unnötig zu bauen.
Sunday thoughts: I'm sure @BastilleBSD would do a better job developing orchestration for jails than k8s 🙂
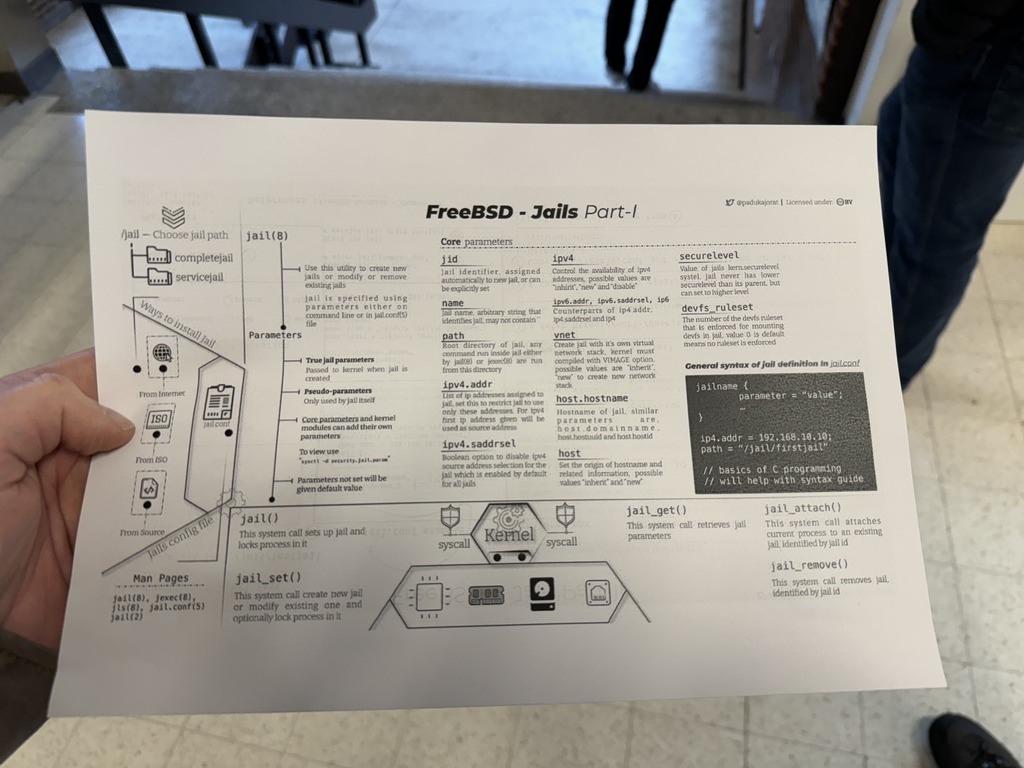
Many thanks to @padukajorat@mastodon.social for providing this great #FreeBSD Jails overview. In three PDFs the basic #Jails functions are shown graphically and explained in more detail.
You can find the PDF hosted on my CDN:
https://cdn.gyptazy.ch/files/docs/freebsd/jails/
This should probably also get included in:
https://wiki.freebsd.org/OnePageTech
All credits to @padukajorat@mastodon.social
ping: @dexter@bsd.network @ozjonty@techhub.social @vermaden@bsd.network (probably sth. for your newsletter to include)
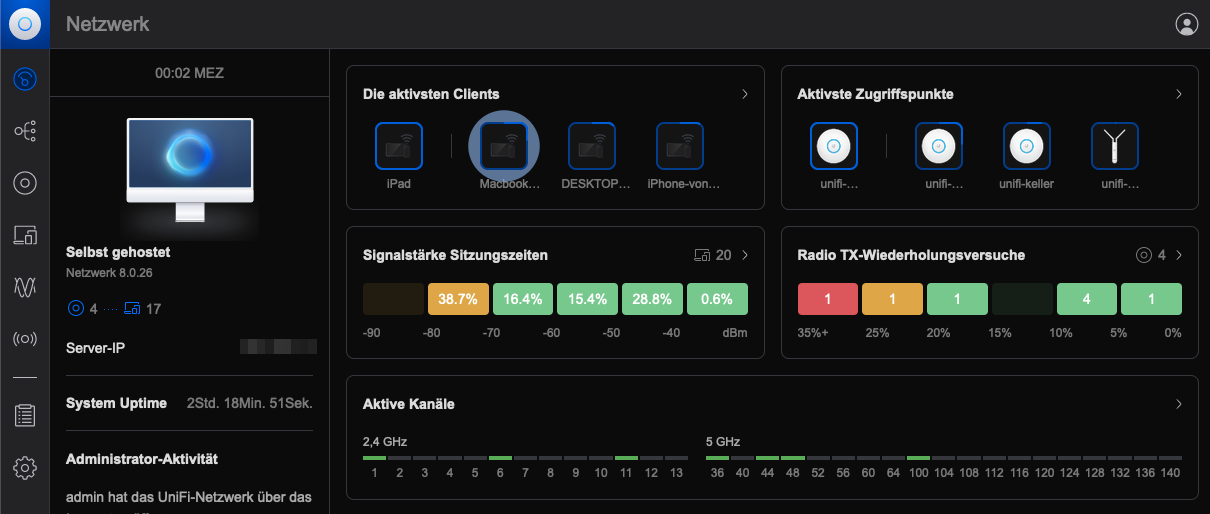
The #UniFi Controller Management Interface enables the management of UniFi devices and the display of network statistics. The installation effort is minimal and quickly completed.
Since #FreeBSD / #TrueNAS #Jails are so lean and FreeBSD is also supported by #Ubiquiti, an installation there is a good idea. A new feature is the storage of the most important data in an external directory and a "Console Only" area.
The Land Before Linux: The Unix desktops • The Register
<https://www.theregister.com/2024/01/27/opinion_column/> @sjvn
❝Today, thanks to Android and ChromeOS, Linux is an important end-user operating system. But, before Linux, there were important Unix desktops, although most of them never made it. …❞
#analysis #Android #Apple #benevolent #cats #Canonical #ChromeOS #consensus #containers #Dell #desktop #dictator #dogs #DragonflyBSD #expert #Flatpak #Foundation #FreeBSD #GhostBSD #GNU #GPL #group #jails #licence #license #Linus #Linux #Mac #Mach #macOS #market #Microsoft #NeXT #NeXTSTEP #opinion #POSIX #share #Slackware #Snap #standards #success #Sun #technology #Torvalds #UNIX #Windows #work #year