Deeply disappointed in the supposed “perimeter defense” tool which solicits CIDR blocks to be scanned but maxes out at 100 IPs, so anything /25 or larger is rejected.
So, I guess I won’t be having them scan our two /21s and various /24s.
I'm hosting a webinar about air-gapped #Nextcloud for organizations with highly confidential data storage and sharing needs.
If that interests you, join me on May 22nd at 9 am EDT / 3 pm CEST to learn about:
🔍 Critical factors to consider
🛡️ Four customizable air-gapped setups
🔧 Setting up air-gapped Nextcloud instances
💼 Best practices for Nextcloud maintenance
Register for free:
https://bit.ly/3QB2dlv
Boosts appreciated 🙏
#OpenSource #infosec #Data #DataProtection #DataSecurity #FOSS
A new attack was published, named TunnelVision, explaining how to snoop all the unencrypted VPN traffic through a local system.
In summary, the attack make the local DHCP server auto configuring workstations network to send a gateway address that is similar to the one used by the VPN but with a higher priority, so the operating system will send its VPN traffic to that address instead of the VPN server.
This attack is not discrete, it could be easily spotted in the network settings.
#Android seems unaffected.
#QubesOS is immune as long as you do not establish a VPN in the qube connected to the real world network (by defaut it's either sys-net or sys-firewall).
#OpenBSD is certainly affected as DHCP option 121 allowing that trick is implemented into dhcpleased (the dhcp client).
However, using a different rdomain for the VPN should prevent any kind of snooping. I wrote a guide explaining how to use WireGuard tunnels on different rdomains https://dataswamp.org/~solene/2021-10-09-openbsd-wireguard-exit.html
Linux users using WireGuard can configure namespaces as a protection: (thanks @zgou for the link)
=> https://www.wireguard.com/netns/
Update1: Tor users do not have to worry, this does not affect Tor at all (it works at a different layer in the network). However, in case you use Tor over VPN, this could potentially leak the fact that you use Tor, but Tor data is still encrypted.
Update2: A properly configured firewall blocking traffic on physical network interfaces when the destination is the VPN server gateway through the tunnel (not the public VPN server IP) will prevent abuse of this vulnerability. Network will be non functional though because the wrong gateway is used and the traffic is blocked.
🔓Maximum-severity GitLab flaw allowing account hijacking under active exploitation
➥ @arstechnica
「 While exploits require no user interaction, hijackings work only against accounts that aren’t configured to use multifactor authentication. Even with MFA, accounts remained vulnerable to password resets, but the attackers ultimately are unable to access the account, allowing the rightful owner to change the reset password 」
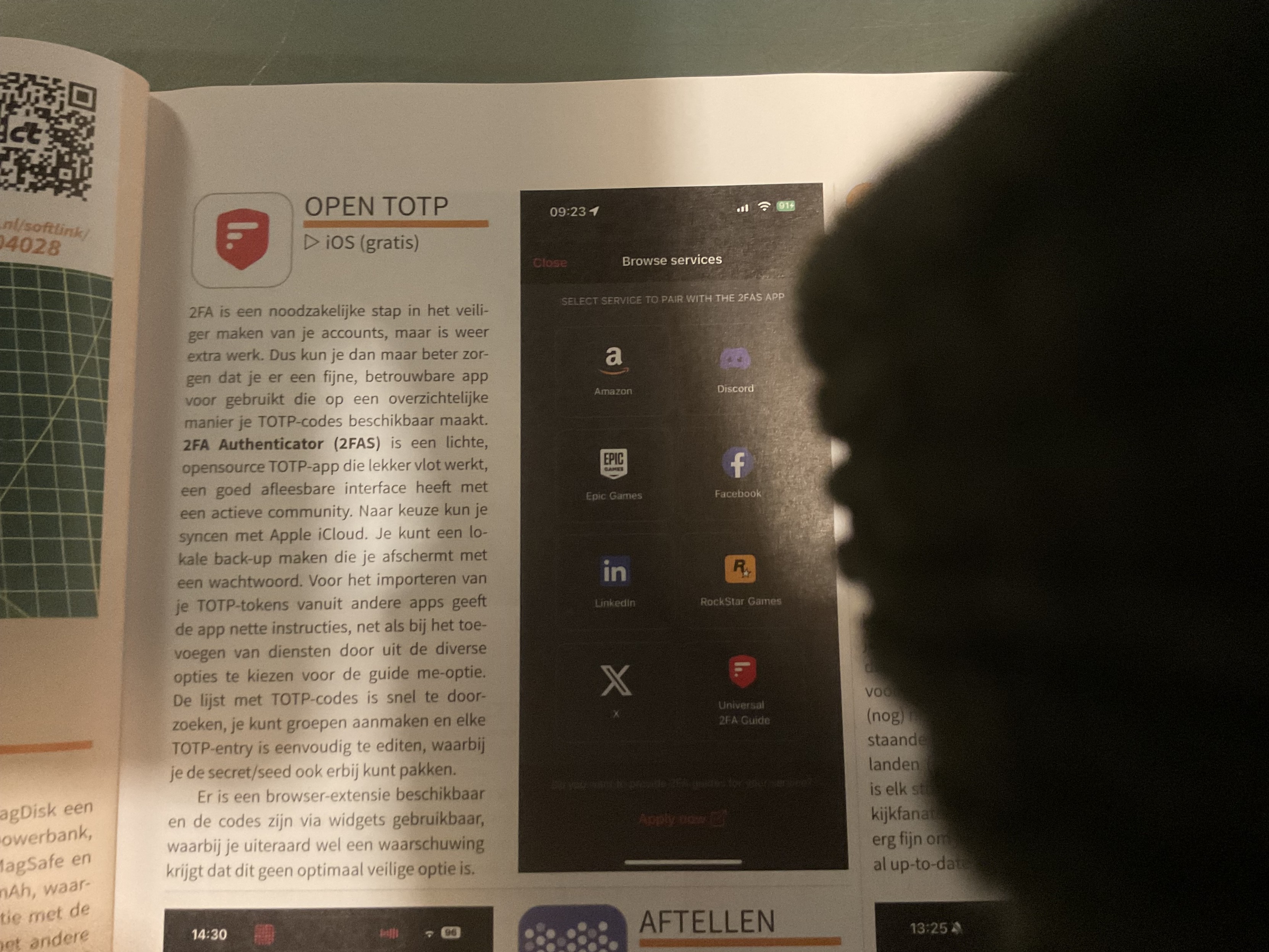
ok, want to use an #opensource #otp app called 2fa authenticator.
To use it you must export your accounts from the other authenticators.
You can do that for 6 other otp apps but not from #microsoft authenticator
Why #microsoft why this behavior.
Microsoft authenticator has no export function for otp
#fail #infosec #otp
Installing DFIR-IRIS on FreeBSD using Jails
This is a live blogging of the installation process of DFIR-IRIS on FreeBSD 14.0-RELEASE using Jails and Jailer.
The main requirements are:
- Nginx
- PostgreSQL
- Python
- Some random dependencies we saw in the Dockerfile
I assume you already have nginx up and running, we will just be setting up a vhost under the domain name dfir.cert.am. Don’t worry, this is INSIDE our infrastructure, you will not be able to connect to it 🙂
First we create a jail named iris0, using Jailer:
jailer create iris0
Next we install the required software inside of the jail. Looks like everything is available in FreeBSD packages:
jailer console iris0<h2>Installing DFIR-IRIS</h2>
pkg install \ nginx \ python39 \ py39-pip \ gnupg \ 7-zip \ rsync \ postgresql12-client \ git-tiny \ libxslt \ rust \ acme.sh
Since we’re using FreeBSD, we’ll be doing things the right way instead of the Docker way, so we will be running IRIS as a user, not as root.
pw user add iris -m
Next we setup some directories and checkout the repo
root@iris0:~ # pw user add iris -m
root@iris0:~ # su - irisiris@iris0:~ $ git clone --branch v2.4.7 https://github.com/dfir-iris/iris-web.git iris-web
Finally, we install some python dependencies using pip.
iris@iris0:~ $ cd iris-web/source
iris@iris0:~/iris-web/source $ pip install -r requirements.txt
Now we have to configure the .env
# -- DATABASEexport POSTGRES_USER=postgresexport POSTGRES_PASSWORD=postgresexport POSTGRES_DB=iris_dbexport POSTGRES_ADMIN_USER=irisexport POSTGRES_ADMIN_PASSWORD=longpasswordexport POSTGRES_SERVER=localhostexport POSTGRES_PORT=5432# -- IRISexport DOCKERIZED=0export IRIS_SECRET_KEY=verylongsecretexport IRIS_SECURITY_PASSWORD_SALT=verylongsaltexport IRIS_UPSTREAM_SERVER=app # these are for docker, you can ignoreexport IRIS_UPSTREAM_PORT=8000# -- WORKERexport CELERY_BROKER=amqp://localhost# Set to your rabbitmq instance# Change these as you need them.# -- AUTH#IRIS_AUTHENTICATION_TYPE=local## optional#IRIS_ADM_PASSWORD=MySuperAdminPassword!#IRIS_ADM_API_KEY=B8BA5D730210B50F41C06941582D7965D57319D5685440587F98DFDC45A01594#IRIS_ADM_EMAIL=admin@localhost#IRIS_ADM_USERNAME=administrator# requests the just-in-time creation of users with ldap authentification (see https://github.com/dfir-iris/iris-web/issues/203)#IRIS_AUTHENTICATION_CREATE_USER_IF_NOT_EXIST=True# the group to which newly created users are initially added, default value is Analysts#IRIS_NEW_USERS_DEFAULT_GROUP=# -- LISTENING PORT#INTERFACE_HTTPS_PORT=443<h2>Configuring HTTPS</h2>
We can use acme.sh to issue a TLS certificate from Lets Encrypt.
root@iris0:~ # acme.sh --set-default-ca --server letsencryptroot@iris0:~ # acme.sh --issue -d dfir.cert.am --standaloneroot@iris0:~ # acme.sh -i -d dfir.cert.am --fullchain-file /usr/local/etc/ssl/dfir.cert.am/fullchain.pem --key-file /usr/local/etc/ssl/dfir.cert.am/key.pem --reloadcmd 'service nginx reload'<h2>Setup nginx</h2>
DFIR-IRIS provides a nginx configuration template at nginx.conf, we will be using that, with a little bit of modifications.
The final nginx.conf will look like this:
#user nobody;worker_processes 1;# This default error log path is compiled-in to make sure configuration parsing# errors are logged somewhere, especially during unattended boot when stderr# isn't normally logged anywhere. This path will be touched on every nginx# start regardless of error log location configured here. See# https://trac.nginx.org/nginx/ticket/147 for more info. ##error_log /var/log/nginx/error.log;##pid logs/nginx.pid;events { worker_connections 1024;}http { include mime.types; default_type application/octet-stream; # Things needed/recommended by DFIR-IRIS map $request_uri $csp_header { default "default-src 'self' https://analytics.dfir-iris.org; script-src 'self' 'unsafe-inline' https://analytics.dfir-iris.org; style-src 'self' 'unsafe-inline';"; } server_tokens off; sendfile on; tcp_nopush on; tcp_nodelay on; types_hash_max_size 2048; types_hash_bucket_size 128; proxy_headers_hash_max_size 2048; proxy_headers_hash_bucket_size 128; proxy_buffering on; proxy_buffers 8 16k; proxy_buffer_size 4k; client_header_buffer_size 2k; large_client_header_buffers 8 64k; client_body_buffer_size 64k; client_max_body_size 100M; reset_timedout_connection on; keepalive_timeout 90s; client_body_timeout 90s; send_timeout 90s; client_header_timeout 90s; fastcgi_read_timeout 90s; # WORKING TIMEOUT FOR PROXY CONF proxy_read_timeout 90s; uwsgi_read_timeout 90s; gzip off; gzip_disable "MSIE [1-6]\."; # FORWARD CLIENT IDENTITY TO SERVER proxy_set_header HOST $http_host; proxy_set_header X-Forwarded-Proto $scheme; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; # FULLY DISABLE SERVER CACHE add_header Last-Modified $date_gmt; add_header 'Cache-Control' 'no-store, no-cache, must-revalidate, proxy-revalidate, max-age=0'; if_modified_since off; expires off; etag off; proxy_no_cache 1; proxy_cache_bypass 1; # SSL CONF, STRONG CIPHERS ONLY ssl_protocols TLSv1.2 TLSv1.3; ssl_prefer_server_ciphers on; ssl_certificate /usr/local/etc/ssl/dfir.cert.am/fullchain.pem; ssl_certificate_key /usr/local/etc/ssl/dfir.cert.am/key.pem; ssl_ecdh_curve secp521r1:secp384r1:prime256v1; ssl_buffer_size 4k; # DISABLE SSL SESSION CACHE ssl_session_tickets off; ssl_session_cache none; server { listen 443 ssl server_name dfir.cert.am; root /www/data; index index.html; error_page 500 502 503 504 /50x.html; add_header Content-Security-Policy $csp_header; # SECURITY HEADERS add_header X-XSS-Protection "1; mode=block"; add_header X-Frame-Options DENY; add_header X-Content-Type-Options nosniff; # max-age = 31536000s = 1 year add_header Strict-Transport-Security "max-age=31536000: includeSubDomains" always; add_header Front-End-Https on; location / { proxy_pass http://localhost:8000; location ~ ^/(manage/templates/add|manage/cases/upload_files) { keepalive_timeout 10m; client_body_timeout 10m; send_timeout 10m; proxy_read_timeout 10m; client_max_body_size 0M; proxy_request_buffering off; proxy_pass http://localhost:8000; } location ~ ^/(datastore/file/add|datastore/file/add-interactive) { keepalive_timeout 10m; client_body_timeout 10m; send_timeout 10m; proxy_read_timeout 10m; client_max_body_size 0M; proxy_request_buffering off; proxy_pass http://localhost:8000; } } location /socket.io { proxy_set_header Host $http_host; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header X-Forwarded-Proto $scheme; proxy_http_version 1.1; proxy_buffering off; proxy_set_header Upgrade $http_upgrade; proxy_set_header Connection "Upgrade"; proxy_pass http://localhost:8000/socket.io; } }}<h2>Setup PostgreSQL</h2>I assume you know how to do this 🙂 You don’t need to configure a separate user, by the looks of it, IRIS likes to do that itself. Thanks to Jails I was able to run a separate PostgreSQL instance in the iris0 jail.
P.S. If you are running PostgreSQL inside a jail, make sure that the following variables are set in your jail configuration
sysvshm = new; sysvmsg = new;<h2>Running DFIR-IRIS</h2>
Now that everything is up and running, we just need to run DFIR-IRIS and it will create the database, needed users, an administration account, etc.
su - iriscd ~/iris-web/source. ../.env~/.local/bin/gunicorn app:app --worker-class eventlet --bind 0.0.0.0:8000 --timeout 180 --worker-connections 1000 --log-level=debug
Assuming everything is fine, now we can setup a rc.d service script to make sure it runs at boot.
For that I wrote two files, the service itself and a helper start.sh script
rc.d script at /usr/local/etc/rc.d/iris
#!/bin/sh# PROVIDE: iris# REQUIRE: NETWORKING# KEYWORD: . /etc/rc.subrname="iris"rcvar="iris_enable"load_rc_config ${name}: ${iris_enable:=no}: ${iris_path:="/usr/local/iris"}: ${iris_gunicorn:="/usr/local/bin/gunicorn"}: ${iris_env="iris_gunicorn=${iris_gunicorn}"}logfile="${iris_path}/iris.log"pidfile="/var/run/${name}/iris.pid"iris_user="iris"iris_chdir="${iris_path}/source"iris_command="${iris_path}/start.sh"command="/usr/sbin/daemon"command_args="-P ${pidfile} -T ${name} -o ${logfile} ${iris_command}"run_rc_command "$1"and the helper script at /home/iris/iris-web/start.sh
#!/bin/shexport HOME=$(getent passwd `whoami` | cut -d : -f 6). ../.env${iris_gunicorn} app:app --worker-class eventlet --bind 0.0.0.0:8000 --timeout 180 --worker-connections 128now we set some variables in rc.conf using sysrc and we can start the service.
sysrc iris_enable="YES"sysrc iris_path="/home/iris/iris-web"sysrc iris_gunicorn="/home/iris/.local/bin/gunicorn"
Finally, we can start DFIR-IRIS as a service.
service iris start
Aaaaand we’re done 🙂
Thank you for reading!
There are some issues that I’d like to tackle, for example, service iris stop doesn’t work, and it would be nice if we ported all of the dependencies into Ports, but for now, this seems to be working fine.
Special thanks to the DFIR-IRIS team for creating this cool platform!
That’s all folks…
https://antranigv.am/posts/2024/05/dfir-iris-freebsd-jail/
#DFIR #FreeBSD #HowTo #InfoSec #IRIS #Jailer #Jails #PostgreSQL #Python
A recent security incident involving Dropbox Sign
https://sign.dropbox.com/blog/a-recent-security-incident-involving-dropbox-sign
Aaah Monday. Time for a new intel #security #sideChannel attack https://pathfinder.cpusec.org/index_files/Pathfinder_HoseinYavarzadeh_ASPLOS24.pdf
I wonder how long it will be before Chinese researchers only report these to the CCP?
The global collaboration in #infosec and #tech in general is declining after Xi Jinping’s rise to power and blockages of free trade by successive US presidents.
[fixed URL]
I'll be at BSides Buffalo on June 1 presenting with one of my extremely talented students about our #cybersecurity CTF team!
#professor #professorlife #academia #academic #academiclife #bsides #bsidesbuffalo #bsidesbuffalo2024 #cybersec #infosec #informationsecurity
Here we see two #Radicle seed nodes, running behind my fully Tor-fied network.
This is a test of exposing a Radicle seed node as a Tor Onion Service endpoint.
These two Radicle nodes are deployed on a #HardenedBSD 14-STABLE VM.
Huge step forward for #HumanRightsTech.
For more information on Radicle (a sovereign {code forge} built on Git): https://radicle.xyz/
Huge shout-out to the Radicle dev team for this collaboration. It has been a blast working with them.
Question to my #infosec bubble:
Do Virtual TPMs in Azure make sense?
Every version of the PuTTY tools from 0.68 to 0.80 inclusive has a critical vulnerability in the code that generates signatures from ECDSA private keys. Tthe effect of the vulnerability is to compromise the private key https://www.chiark.greenend.org.uk/~sgtatham/putty/wishlist/vuln-p521-bias.html #infosec #security #ssh #opensource #linux #unix #windows
Lol so many ignorants on the recent vulnerabilities about command injection.
Btw, it is not just Rust affected. It affects most langs. Rust is the only one who cares and released a security advisory
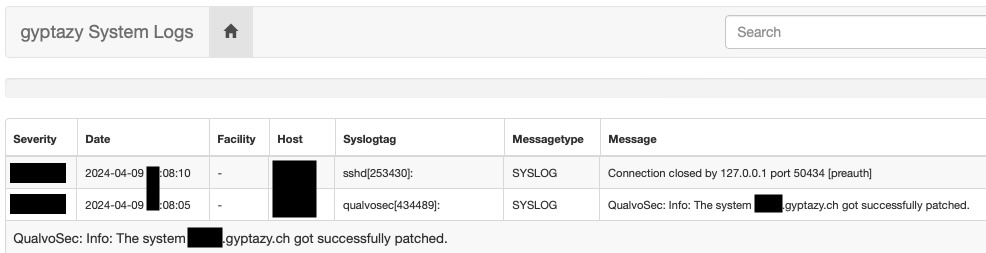
#SecurityPatchManagement tools like #QualvoSec may help integrating automated security patches.
#infosec #linux #BSD #Debian #RockyLinux #CentOS #RedHat #FreeBSD #patchManagement #SecurityPatching #Patching
How the XZ backdoor works https://lwn.net/SubscriberLink/967192/6c39d47b5f299a23/ #linux #infosec #security
Decade-Old #Linux 'wall' Bug Helps Generate Fake SUDO Prompts, Threatens Password Security
https://linuxsecurity.com/news/security-vulnerabilities/linux-wall-bug
#InfoSec
Yikes… upstream xz/lzma repository compromised, hostile code injected into sshd in distros with newer packages https://www.openwall.com/lists/oss-security/2024/03/29/4
The code for the program that toggles exploit mitigations and security hardening techniques in #HardenedBSD has been rewritten from scratch.
This rewritten version will land in 15-CURRENT no later than the end of this month/weekend:
https://groups.google.com/u/1/a/hardenedbsd.org/g/users/c/6Z7Rx9cOg7s
This change is transparent to users. The only folks that might be affected are those who consume the libhbsdcontrol library directly. The ABI and API have both been changed.
The command-line arguments to the hbsdcontrol(8) utility are unchanged.
I await the day when vulnerabilities have their own colognes.
"This vulnerability smells like sweaty gym socks."
I'll be giving a presentation on #HardenedBSD today in Denver, Colorado at 6:30pm. If you're interested in #FreeBSD, #infosec, and/or #HumanRightsTech, I'd love for you to come join me.
It does indeed look like extattr_get_fd(2) is broken in a Capabilities-enabled process, even for file descriptors with the CAP_EXTATTR_GET capability set:
https://lists.freebsd.org/archives/freebsd-hackers/2024-March/003104.html
A capable colleague passed on a request from their client. They want to know if the VM disks are encrypted at rest, if the keys are rotated periodically, and if there's a key retention procedure in place. Ironically, the client's VPS runs on Ubuntu 18.04, which has been out of updates for a year, and despite numerous notifications to upgrade, they believe it can wait. 😄
#CyberSecurity #Encryption #DataProtection #Ubuntu #VPS #TechSupport #InfoSec
#QualvoSec's upcoming features:
- whitelist (packages to update only)
- blacklist (package to refuse from being upgraded)
- API (list of installed packages & versions on nodes)
- Multiple patch windows
- Grouping
- First iteration of (the still very limited) admin tool
#patchmanagement #security #infosec #debian #freebsd #rockylinux #redhat #ubuntu #BSD #securitypatchmanagement #Fedora
I'll be giving a practice run of my presentation titled "HardenedBSD 2024 State of the Union: A Decade of Hardened Bits" on March 23rd, 2024 up in Denver, Colorado: https://www.meetup.com/dc303denver/events/298257710/
If you're in the greater Denver area and interested in #BSD or #infosec, I would love for you to join and give me feedback.
#SoldierX has a new code hosting partner: #HardenedBSD. The first project being hosted is #libhijack: https://git.hardenedbsd.org/SoldierX/libhijack
It is my pleasure to appoint you to serve on the Cybersecurity and Infrastructure Security Agency (CISA) Cybersecurity Advisory Committee (CSAC) Technical Advisory Council (TAC) subcommittee. Thank you for volunteering to support this important effort.
The TAC subcommittee is tasked with providing recommendations for full Committee deliberation and vote to further explore how CISA, in line with their Secure by Design goals, can encourage companies to be better stewards of the open source software they depend on and produce
This is going to be a lot of fun! I'm happy and honored to work with knowledgeable, talented peers with unique insights. I'm grateful for the opportunity.
#sysadmin and #infosec check this out. #QualvoSec looks promising:
Also limiting the number of recursions in this directory removal function: https://git.hardenedbsd.org/hardenedbsd/HardenedBSD/-/commit/148478d5743a8dd4362fd31dca4371618716d0a8
This #HardenedBSD commit fixes two potential NULL pointer derefs in the new pam_xdg(8) #FreeBSD PAM module: https://git.hardenedbsd.org/hardenedbsd/HardenedBSD/-/commit/0b5bf32630b3429e0b5a321e6621a404dc93ecc5
edit[0]: Fixed a typo in a follow-up commit: https://git.hardenedbsd.org/hardenedbsd/HardenedBSD/-/commit/865994a5cf20937224bde0662bb1f96ba18e072f
Lightly tested new build of #hbsdfw released: https://hardenedbsd.org/~shawn/hbsdfw/hbsdfw_installer_vga_14.0-20240223-222012.iso.xz
Your usual upgrade instructions:
- Back up your configuration
- Reinstall from scratch
- Restore configuration file
Default username/password: root/hbsdfw
hbsdfw is a #HardenedBSD 14-STABLE fork of #OPNsense.
edit[0]: Add usual upgrade instructions.
edit[1]: Add default username and password
Proper redaction is hard to do in #git : https://github.com/tenable/poc/commit/28634effa93cfeb941a0a526290c6e4758d97d5a
Hi there, folks. I've moved back to #Fosstodon yet again.
I'm a #DevOps guy, who used to be a Linux #sysadmin for many years before that. I run #OpenBSD  and #GrapheneOS
and #GrapheneOS  on my personal devices.
on my personal devices.
I post random thoughts and dumb jokes. And I think up unlikely #infosec vulnerabilities.
Purely from an #infosec point of view I am eagerly awaiting details about this exploit.
Transparency is key in these situations. How #Mastodon handles this in the coming days will be telling, but the CVE publish is already a good sign.
https://github.com/mastodon/mastodon/security/advisories/GHSA-3fjr-858r-92rw
Interesting new commit in #HardenedBSD:
HBSD: Provide support for prohibiting new USB device connectionsThis commit introduces the hardening.pax.prohibit_new_usb sysctl
tunable node. This node can be set to one of three values:
0: Disabled
1: Enabled
2: Enabled without possibility to disable
When set to 2, a reboot is required to end the prohibition on new USB
connections.
This is based on a patch by Loic F <loic.f@hardenedbsd.org>.








 🎸 🏳️🌈 ⏚
🎸 🏳️🌈 ⏚