Quick #DNS study on #CAA records. Taking the ~192 entries in the list of possible identifers in CAA records, which are domain names loosely identifying CAs, gives 168 distinct domains... on which only 41 do have at least one issue/issuewild CAA record on them! With 24 of those 41 to have themselves as CAA records, but often with other names, hence other CAs. And also obvious errors in CAA records, like using "www.digicert.com" where correct is "digicert.com".
#DNS #EuDotOrg #DNSSEC
J'arrive pas à saisir mon enregistre DNSKEY pour le domaine que j'essaye de saisir, j'ai le message suivant.
L'enregistrement DS demandé ne correspond à aucune DNSKEY publiée
Pourtant, la commandedrill DNSKEY trans13nrv.eu.org lancé depuis une machine extérieure à mon serveur faisant autoritaire, me donne le résultat suivant:
(…)
trans13nrv.eu.org. 3600 IN DNSKEY 257 3 13 e0Org7Of/JK6J5LZTLnGPVLn3fR01wedEfNS0E66CDCM+0qZpwORpQjL dyoB7TVPvs2Y4SVgDQiPSy+v2M6Orw==
(…)
Elle est donc bien publique.
quelqu'un chez eu.org aurait une idée?
Le boost est très apprécié!
Setting up DNSCrypt was easier than anticipated on my Debian machine without systemd-resolved. I really like the binary distribution, which is available as a self-contained directory with the binary and sample configuration. You can run the whole thing from that portable directory and move it around or specify locations on the command line if you wanna spread it.
Also, the gradual and modular approach to the generic Linux installation was a delight to follow, always being reminded to take small and verifiable steps along the way.
For anyone interested, this is it: https://github.com/DNSCrypt/dnscrypt-proxy/wiki/Installation-linux
#DNSCrypt #DNSSEC #DNS #sysadmin #debian #netsec #networksecurity #it
# telnet mx2.ipoac.nl 25 -4
Trying 86.80.166.233...
telnet: Unable to connect to remote host: Network is unreachable
# telnet mx2.ipoac.nl 25 -6
Trying 2a02:a46f:95b7::1...
Connected to mx2.ipoac.nl.
220 mx2.ipoac.nl ESMTP Postfix
Just amazing that my cable #isp #ziggo blocks tcp dport 25 outbound over #ipv4, but #ipv6 is fine apparently.
Still not very useful with a fixed reverse #DNS that ends in cable.dynamic.v6.ziggo.nl that #spamfilters seem to love.
If #DNS is so great, why is there a .int, but not a .float, .char, or .double? 🤔
I was able to diagnose a DNS issue because I had my Unbound server sending queries to a remote syslog server.
The PBS video player requires that imasdk.googleapis.com. be allowlisted if it's contained in your DNS-based adblock list.
It was easy to spot by:
$ tail -F /var/log/network/dns-01/2024-04/all.log | grep -F 192.168.1.102
That told me what the client system (192.168.1.102) was trying to resolve in real-time.
Software author: NEVER NEVER NEVER use a dummy, non-existing domain in the default configuration, it may exist one day! https://crapts.org/2024/04/21/all-fritz-box-modems-have-been-hijacked/
Has anyone tried dns0.eu yet?
https://www.dns0.eu/zero
@jhx For writing some kind of "howto", I'll have to find a sane scope ... otherwise there would be just too much to describe I guess 😮
I could of course assume you already have
- network segmentation with a #DMZ
- a working "domain" setup with a directory and #DNS (e.g. #samba, but could be #OpenLDAP with #bind9 as well)
- (virtual) machines providing #RDP (with #xrdp in case of #Linux or #FreeBSD)
- a working mechanism to distribute X.509 #TLS #certificates (I request them from #letsencrypt using #uacme and distribute them with simple shell scripts using special-purpose restricted #SSH keys)
With all that in place, it would "just" be describing the setup of #guacamole in a #FreeBSD #jail, enabling #TLS on all connection paths...
@jhx For writing some kind of "howto", I'll have to find a sane scope ... otherwise there would be just too much to describe I guess 😮
I could of course assume you already have
- network segmentation with a #DMZ
- a working "domain" setup with a directory and #DNS (e.g. #samba, but could be #OpenLDAP with #bind9 as well)
- (virtual) machines providing #RDP (with #xrdp in case of #Linux or #FreeBSD)
- a working mechanism to distribute X.509 #TLS #certificates (I request them from #letsencrypt using #uacme and distribute them with simple shell scripts using special-purpose restricted #SSH keys)
With all that in place, it would "just" be describing the setup of #guacamole in a #FreeBSD #jail, enabling #TLS on all connection paths...
If got a #DummyQuestion. At least it feels like I should know.
How do I get the registrar information of a (#DNS) domain?
Edit:
The concrete domain are:
- sm-q.de (faking sma.de)
- sma-amerrica.com (faking sma-america.com)
Most of the time I succeed with #WHOIS. But sometimes the WhoIs record doesn't contain the information. Is there a better way?
Context: analyzing lookalike domain used for scams
#Ed25519 or #ECDSA-P256 or still on some #RSA algorithms? Shorter key length is especially in DNS a benefit but still not all resolvers may be able to support this in 2024?!
A good example of cooperation between #OSS projects and the responsible handling of security vulnerabilities is probably the handling of https://www.cve.org/CVERecord?id=CVE-2023-50868. Several projects have worked together on solutions and simultaneously published the secured versions and information on the problems. If I have a good overview of all this, you can give a lot of praise for this. Especially when it comes to an important building block of the free Internet like #DNS. #BIND #PowerDNS #UnBound
What I don't expect if the first email after the "can you liaise" one being "can you change the A record to x.x.x.x as soon as possible"
garrrr, does nobody else plan these things? just do it and hope for the best? FFS
@gyptazy At least for #DNS, the answer is clearly no: https://indico.dns-oarc.net/event/48/contributions/1047/
New multi-implementation DNSSEC validation DoS vulnerabilities - CVE-2023-50387 ("KeyTrap"), CVE-2023-50868 (NSEC3 vuln)
(living doc, updated regularly - if you prefer a low-edit post to boost, use https://infosec.exchange/@tychotithonus/111926621712441626)
Looks like DNS-OARC coordinated fixes in advance, but I don't see a centralized analysis, other than this announcement from the team who discovered KeyTrap:
https://www.athene-center.de/en/news/press/key-trap
(Details may be still partially embargoed until patching ramps up)?
Analysis:
DoS of all major DNSSEC-validating DNS resolvers (servers, but also maybe local resolvers like systemd's?) at the implementation level. Exploitation described as 'trivial'. Both are CVSS 7.5. DNS is a rich ransom target - but some resolver setups don't even validate DNSSEC.
"In 2012 the vulnerability made its way into the implementation requirements for DNSSEC validation, standards RFC 6781 and RFC 6840" (per ATHENE)
Per the Unbound writeup, both vulns require query to a malicious zone (which is probably not hard to trigger, for any DNSSEC-enabled client or server).
Resolution: patch (recommended); disable DNSSEC validation (discouraged, but can buy you time / mitigate active DoS)
Fixes mitigate the exhaustion by putting caps on validation activities. These caps appear to have been missing from most implementations.
Details:
Two DNSSEC DoS CVEs:
CVE-2023-50387 ("KeyTrap"): "DNSSEC verification complexity can be exploited to exhaust CPU resources and stall DNS resolvers" (CVSS 7.5)
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H
https://seclists.org/oss-sec/2024/q1/125
(KeyTrap was discovered by ATHENE - their press release here has very important detail:
https://www.athene-center.de/en/news/press/key-trap)
CVE-2023-50868: "NSEC3 closest encloser proof can exhaust CPU" (CVSS 7.5)
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H
MITRE links (now populated):
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-50387
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-50868
Vulmon queries:
https://vulmon.com/searchpage?q=CVE-2023-50387
https://vulmon.com/searchpage?q=CVE-2023-50868
VulDB:
https://vuldb.com/?id.253829
Patch status:
ISC BIND (patched - vuln since 2000?):
https://fosstodon.org/@iscdotorg/111924416653890048
https://kb.isc.org/docs/cve-2023-50387
https://kb.isc.org/docs/cve-2023-50868
https://seclists.org/oss-sec/2024/q1/125
https://www.isc.org/blogs/2024-bind-security-release/
(note: posts say "Versions prior to 9.11.37 were not assessed." but also have a range of affected versions starting at 9.0.0 - typo?)
Unbound (patched - vuln since Aug 2007):
https://nlnetlabs.nl/news/2024/Feb/13/unbound-1.19.1-released/
https://nlnetlabs.nl/downloads/unbound/CVE-2023-50387_CVE-2023-50868.txt
https://seclists.org/oss-sec/2024/q1/126
dnsmasq (patched - 2.90 has fix):
https://thekelleys.org.uk/dnsmasq/CHANGELOG
https://lists.thekelleys.org.uk/pipermail/dnsmasq-discuss/2024q1/017430.html
Knot (patched in 5.7.1):
https://www.knot-resolver.cz/2024-02-13-knot-resolver-5.7.1.html
pfSense:
(Bundled Unbound: plan appears to be to make a separate package available for manual update?; BIND: optional package)
https://forum.netgate.com/topic/186145/unbound-cve-2023-50387-and-cve-2023-50868/1
https://redmine.pfsense.org/issues/15256
Pi-Hole (uses dnsmasq - patch available)
https://www.patreon.com/posts/dnssec-fix-98498055
https://pi-hole.net/blog/2024/02/13/fixing-two-new-dnssec-vulnerabilities/
PowerDNS (patched - all versions affected):
https://blog.powerdns.com/2024/02/13/powerdns-recursor-4-8-6-4-9-3-5-0-2-released
https://github.com/PowerDNS/pdns/pull/13781
https://github.com/PowerDNS/pdns/pull/13784
https://seclists.org/oss-sec/2024/q1/130
systemd.resolved:
[?]
OS status:
Fedora:
https://bodhi.fedoraproject.org/updates/FEDORA-2024-e24211eff0
FreeBSD:
https://cgit.freebsd.org/ports/commit/?id=58e048cad653819eebf91af5840e4b00f155bb1b
Gentoo:
https://bugs.gentoo.org/show_bug.cgi?id=CVE-2023-50387
Red Hat:
https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2023-50387
https://access.redhat.com/security/security-updates/cve [?]
SUSE:
https://bugzilla.suse.com/show_bug.cgi?id=1219823
Ubuntu:
https://ubuntu.com/security/CVE-2023-50387
https://ubuntu.com/security/CVE-2023-50868
https://ubuntu.com/security/notices/USN-6633-1
Windows (Server, DNS Role):
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-50387
Package status:
BIND:
https://repology.org/project/bind/versions
dnsmasq:
https://repology.org/project/dnsmasq/versions
Unbound:
https://repology.org/project/unbound/versions
GitHub:
https://github.com/advisories/GHSA-8459-gg55-8qjj
Go (Knot module?)
https://github.com/golang/vulndb/issues/2552
Non-coverage: (no mentions known yet)
Akamai
https://www.akamai.com/blog [?]
AWS
[?]
Azure (Microsoft Server DNS?)
[?]
Cisco Umbrella:
https://umbrella.cisco.com/blog [?]
Cloudflare
https://blog.cloudflare.com/ [?]
CoreDNS
https://coredns.io/blog/ [?]
Google DNS
[?]
(The Register article (see below) says Google is aware)
Infoblox
https://blogs.infoblox.com/ [?]
Quad9 DNS
https://www.quad9.net/news/blog/ [?]
News/Press
https://www.theregister.com/2024/02/13/dnssec_vulnerability_internet/
https://www.securityweek.com/keytrap-dns-attack-could-disable-large-parts-of-internet-researchers/
Detection/Validation:
Check to see if a server is doing DNSSEC validation (if not an open recursive resolver, you may need to query a zone the server is authoritative for):
# zone signed, server DNSSEC-enabled:
$ delv example.net @8.8.8.8
; fully validated
example.net. 4437 IN A 93.184.216.34
example.net. 4437 IN RRSIG A 13 2 86400 20240225232039 20240204162038 18113 example.net. 94G2PRXins1G9ntfklvCq2mvcgqjB0z9FqQXp77lD/wXR4J3D67ceih1 yNgsYYqlIAOoWKXUekux6Zq9aIwszQ==# zone unsigned, server DNSSEC-enabled:
$ delv google.com @8.8.8.8
; unsigned answer
google.com. 100 IN A 142.250.69.206
Tenable:
https://www.tenable.com/plugins/pipeline/issues/165587
Exploits:
(none yet known / public, but multiple sources describe as "trivial")
#keytrap #nsec3 #CVE202350387 #CVE202350868 #CVE_2023_50387 #CVE_2023_50868
#dns #dnssec
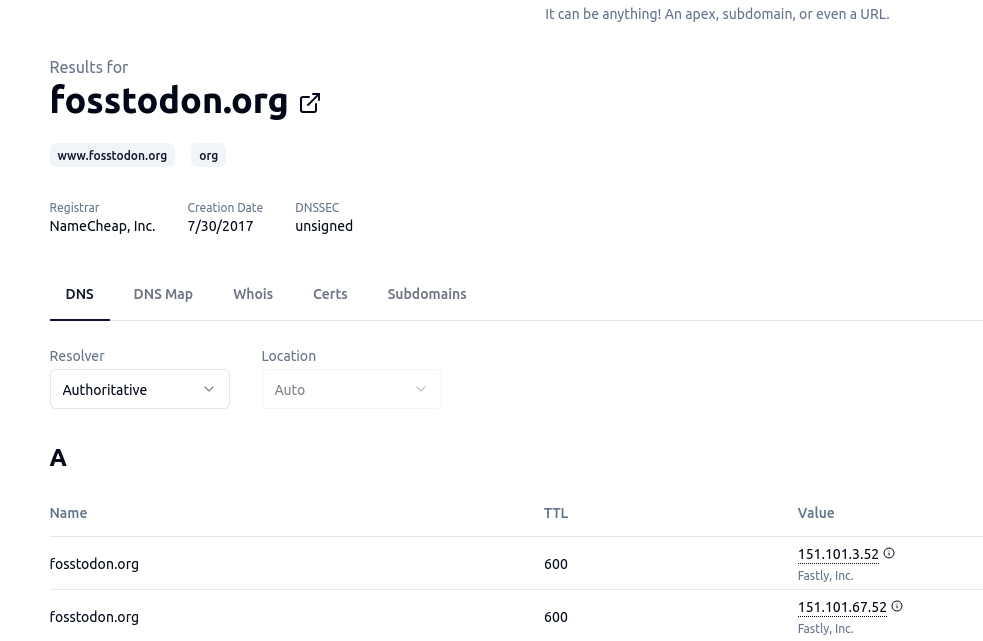
For my #DNS friends, this looks like a pretty neat way of doing DNS/Domain queries on the web - it does a lot more than just port 53. https://digger.tools/ Also available as source on GitHub
Hmmm. I was playing with #OpenSSH's Host Key Rotation feature (https://blog.djm.net.au/2015/02/key-rotation-in-openssh-68.html) and publishing the new and old keys as #SSHFP in the #dns.
However, I noticed that the OpenSSH client would only check the primary key offered, and if _any_ of the SSHFP keys didn't match (which, they would not by definition), then it would shout that the already-cached host keys didn't match.
This seems to be intentional, but did surprise me a bit. I was hoping to preload all of the keys, so clients would have an easier upgrade process.
(OpenSSH server 9.5, client 9.6; both as part of #OpenBSD)